Critical Infrastructure Under Threat: Essential Action Steps for Securing Critical Infrastructure and Operational Resilience
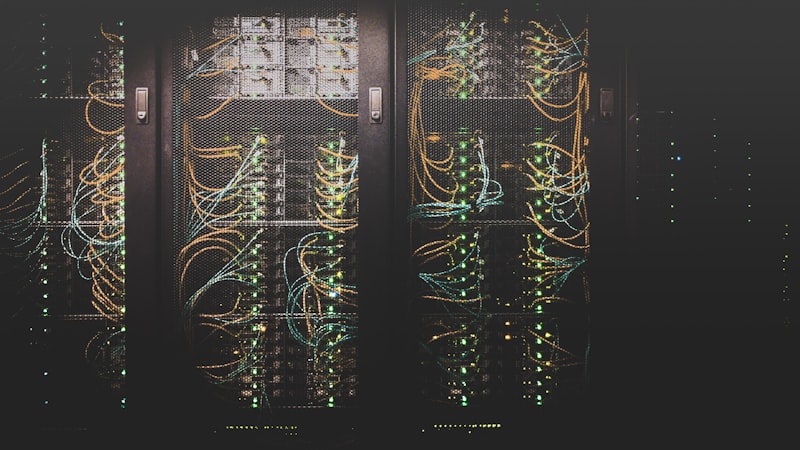
In an era where our critical infrastructure faces unprecedented threats, decisive action is imperative. We must prioritize robust cybersecurity measures and fortify our operational resilience to safeguard essential services and protect our communities. Together, we can rise to the challenge and secure a safer future for all.
Recent intelligence from CISA and the FBI reveals an alarming surge in sophisticated cyber threats targeting critical infrastructure sectors. From business email compromise schemes diverting millions from construction projects to ransomware attacks paralyzing healthcare systems, the threat landscape has never been more complex or consequential. This analysis provides actionable intelligence and specific defensive measures to protect your organization’s assets, operations, and reputation.
Business Email Compromise: A $2.9 Billion Threat to Construction and Supply Chains
The FBI has identified a coordinated Business Email Compromise (BEC) campaign specifically targeting construction companies and their business partners. This attack vector has become increasingly problematic, with BEC schemes causing $2.9 billion in losses during 2023 alone, making it the second most costly cyberattack method.
The construction industry is particularly vulnerable due to its high-value transactions and complex stakeholder networks. Attackers follow a consistent pattern:
- Research projects to identify suitable targets and associated companies
- Register domains deceptively similar to legitimate construction companies (e.g., FamousConstruction.com vs. FamousContractors.com)
- Send carefully crafted emails requesting Automated Clearing House or Direct Deposit detail changes
- Divert payments to fraudulent accounts controlled by the threat actors
Losses from these attacks range from five figures to over one million dollars per incident. What’s particularly concerning is that these fraudulent transfers may continue for extended periods before detection, as audit cycles often lag behind payment schedules.
Actionable Steps to Prevent BEC Attacks
Implement strict verification protocols for payment changes:
- Mandate secondary channel verification for all payment information changes (call a known contact number rather than relying solely on email)
- Flag any “urgent” requests for payment changes as potentially suspicious
- Establish multi-person approval workflows for financial transactions over specific thresholds
Strengthen technical controls:
- Deploy multi-factor authentication (MFA) for all email accounts, especially those with financial authority
- Implement email authentication protocols (SPF, DKIM, DMARC) to prevent domain spoofing
- Configure email filters to flag messages from similar-but-not-identical domains
Conduct regular security awareness training:
- Train employees to scrutinize email addresses (using CTRL+F to check exact matches against known contacts)
- Teach staff to question unexpected payment change requests, especially those that bypass normal processes
- Simulate BEC attacks to test employee responses and reinforce training
Monitor and respond:
- Implement automated systems to monitor for irregular payment patterns or new recipients
- Establish a swift incident response plan for potential BEC incidents
- Conduct regular assessments of payment verification procedures
Business Value of BEC Prevention
Implementing these measures delivers a substantial return on investment. With the average BEC attack costing $125,000 and the average breach remediation approaching $5 million, prevention is significantly more cost-effective than recovery. Additionally, protecting payment systems maintains operational continuity and preserves relationships with vendors and clients.
Biosecurity Risks: Protecting Biological Materials and Intellectual Property
A concerning trend involving visiting foreign researchers removing biological materials from university and private sector laboratories has emerged. This activity creates dual risks: loss of intellectual property and potential biosecurity incidents affecting public health.
Approximately 1,500 state-owned and commercial culture collections worldwide maintain, exchange, and sell samples of microbes and toxins. About one-third of collections outside the United States potentially house dangerous pathogens without adequate security controls. This vulnerability extends to research facilities where visiting scientists can access valuable biological materials.
Actionable Steps to Enhance Biosecurity
Implement a layered physical security approach:
- Establish perimeter controls with electronic access points
- Secure building entrances with electronic access control
- Add additional access restrictions to laboratory spaces
- Lock biological agent storage units (freezers) and sensitive areas
- Install video surveillance in key locations
Establish robust material accountability systems:
- Maintain detailed inventories of biological materials
- Document all material transfers with proper verification
- Implement secure tracking systems for biological samples
- Require dual authorization for access to high-risk materials
Strengthen personnel controls:
- Conduct background investigations for all staff working with biological materials
- Implement periodic reinvestigation for personnel with access to secure areas
- Verify references and credentials for visiting researchers
- Establish clear protocols for visitor supervision and material handling
Integrate cyberbiosecurity practices:
- Secure cyber and cyber-physical systems in laboratories
- Protect building automation systems that control ventilation, pressurization, and containment
- Implement cybersecurity measures for laboratory equipment and data systems
- Establish access controls for digital research information
Medusa Ransomware: A Growing Threat to Critical Infrastructure
The FBI, CISA, and MS-ISAC have issued a joint advisory on Medusa ransomware, a sophisticated ransomware-as-a-service (RaaS) variant that has impacted over 300 victims across critical infrastructure sectors since its emergence in June 2021.
Medusa’s impact varies by sector but is uniformly devastating:
- Healthcare facilities face delays in patient care as systems become locked, potentially risking lives
- Educational institutions lose access to essential records and learning platforms
- Manufacturing operations experience production halts, leading to supply chain disruptions
- Technology companies suffer breaches that expose sensitive intellectual property
The frequency of Medusa attacks has increased by 42% since 2023, reflecting its growing sophistication and adaptability. The ransomware employs a double-extortion model, encrypting data and threatening to leak stolen information if demands aren’t met.
Medusa’s Attack Methods
Medusa gains initial access through multiple vectors:
- Vulnerability exploitation: Microsoft Exchange Server (ProxyShell, CVE-2021-34473), ScreenConnect Authentication Bypass (CVE-2024-1709), Fortinet EMS SQL Injection (CVE-2023-48788)
- Compromised remote services: Using stolen RDP credentials often purchased from Initial Access Brokers (IABs), exploiting poorly secured VPN connections
- Phishing campaigns: Spear-phishing emails to steal credentials or deploy malware
Once inside, attackers move laterally using legitimate tools such as AnyDesk, ConnectWise, and Splashtop, making detection challenging.
Actionable Steps to Mitigate Medusa Ransomware Risk
Implement robust vulnerability management:
- Patch critical vulnerabilities promptly, especially those exploited by Medusa
- Deploy comprehensive vulnerability scanning tools
- Prioritize CVE-2024-1709, CVE-2023-48788, and CVE-2021-34473
Strengthen network security:
- Segment networks to prevent lateral movement
- Implement strict access controls based on least privilege principles
- Monitor and block suspicious east-west traffic
- Filter network traffic from untrusted sources
Enhance endpoint protection:
- Deploy Endpoint Detection and Response (EDR) solutions
- Utilize application allow listing to prevent unauthorized programs from executing
- Monitor for suspicious PowerShell and WMI activity
- Disable unnecessary command-line capabilities
Establish comprehensive backup protocols:
- Maintain regular, offline backups of critical data
- Test backup restoration processes regularly
- Implement the 3-2-1 backup strategy (three copies, two different media types, one off-site)
- Ensure backups are encrypted and immutable
Strengthen email security:
- Implement robust email filtering to detect phishing attempts
- Train employees to recognize social engineering tactics
- Block executable attachments and potentially dangerous file types
Business Value of Ransomware Mitigation
The financial incentive for implementing these measures is compelling. The average ransomware recovery cost soared 500% to $2.73 million in 2024, far exceeding the investment required for preventive measures. Beyond the direct financial impact, ransomware attacks cause significant operational disruption, with businesses averaging 21 days of downtime following an attack.
Critical Vulnerabilities Requiring Immediate Action
CISA has added two significant vulnerabilities to its Known Exploited Vulnerabilities Catalog, both actively being exploited in the wild:
CVE-2025-24472: Fortinet FortiOS and FortiProxy Authentication Bypass
This high-severity vulnerability (CVSS 8.1) affects FortiOS versions 7.0.0 through 7.0.16 and FortiProxy versions 7.0.0 through 7.0.19/7.2.0 through 7.2.12. It allows remote attackers to gain super-admin privileges via crafted CSF proxy requests.
Threat actors are exploiting this vulnerability to:
- Create rogue admin or local users
- Modify firewall policies
- Access SSL VPNs to gain entry to internal networks
Remediation: Upgrade to FortiOS 7.0.17 or above, FortiProxy 7.0.20/7.2.13 or above.
CVE-2025-30066: tj-actions/changed-files GitHub Action Vulnerability
This vulnerability affects a GitHub Action used in over 23,000 repositories. Attackers injected malicious code that downloads a Python script designed to scan for and extract credentials and secrets, including AWS keys, GitHub tokens, and RSA keys.
Remediation: Remove public access temporarily, replace affected actions, and rotate any potentially compromised secrets.
Industrial Control Systems: Protecting the Operational Technology Backbone
CISA has released seven new Industrial Control Systems (ICS) advisories covering vulnerabilities in Schneider Electric, Rockwell Automation, and Mitsubishi Electric systems. These vulnerabilities potentially impact critical operational technology environments that control essential infrastructure.
Key Vulnerabilities and Impacts
- ICSA-25-077-01: Schneider Electric EcoStruxure Power Automation System UI - An improper authentication vulnerability (CVE-2025-0813, CVSS v4: 7.0) that allows attackers to bypass device authentication when they have physical access.
- ICSA-25-077-02: Rockwell Automation Lifecycle Services with VMware - Multiple high-severity vulnerabilities, including TOCTOU race condition, that could potentially allow access to both OT and IT systems.
Actionable ICS Security Measures
- Implement a multi-type mitigation strategy: Move beyond patch-only approaches to include network-based mitigation, identity and access controls as compensating controls, and network segmentation.
- Adopt a defense-in-depth approach: Segment ICS networks from corporate and external networks, implement role-based access control, deploy intrusion detection systems specific to OT environments.
- Align with established frameworks: Adopt standards such as NIST CSF, ISA/IEC 62443, or CIS Controls for ICS.
Business Value of ICS Security
Unplanned downtime in industrial environments costs an average of $250,000 per hour, making preventive security measures highly cost-effective. Organizations with mature ICS security programs report 63% fewer safety incidents and 23% greater operational efficiency.
Conclusion: Integrating Security into Business Strategy
The threat landscape facing critical infrastructure has never been more complex or consequential. By implementing the actionable steps outlined in this analysis, critical infrastructure organizations can significantly reduce their risk exposure while enhancing operational resilience. The business value extends far beyond mere loss prevention:
- Operational continuity ensures uninterrupted delivery of critical services
- Financial protection from both direct losses and remediation costs
- Regulatory compliance reduces the risk of penalties and enforcement actions
- Reputational preservation maintains stakeholder and customer trust
- Competitive advantage through demonstrated resilience and reliability
The most effective approach is to integrate these security measures into broader business strategies rather than treating them as isolated technical requirements. By aligning security investments with business objectives, organizations can maximize return on investment while building sustainable resilience against evolving threats.
As we’ve demonstrated, the cost of prevention is invariably lower than the cost of recovery. In today’s threat landscape, proactive security isn’t just good practice – it’s good business.
Related Posts
 Cybersecurity
CybersecurityCybersecurity for Critical Infrastructure: Protecting Essential Systems
Critical infrastructure faces growing cyber threats. This blog delves into the changing risks and highlights essential …
 AI
AIThe AI Minefield: AI Security, Privacy, and Data Risks in Professional and Personal Use
AI's rapid adoption outpaces awareness of its hidden risks. This blog unpacks evolving threats and equips you with …
