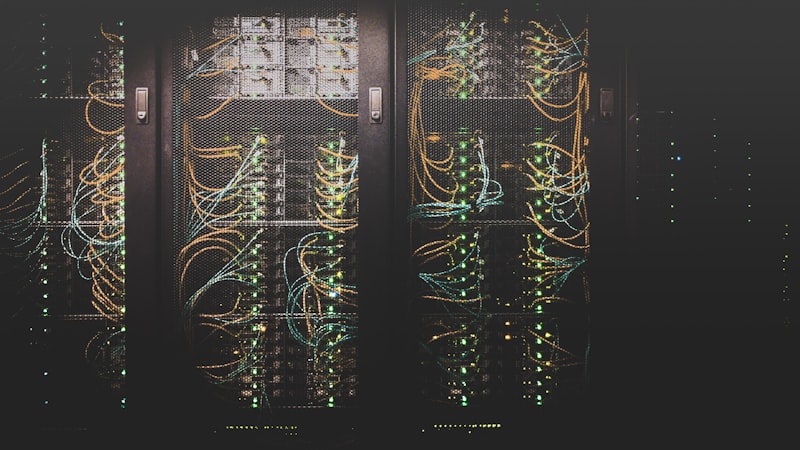
 Cybersecurity
CybersecurityMethods for Securing Critical Infrastructure
Protecting critical infrastructure is a complex and essential task. Implementing effective infrastructure security …
17 posts
 Cybersecurity
CybersecurityProtecting critical infrastructure is a complex and essential task. Implementing effective infrastructure security …
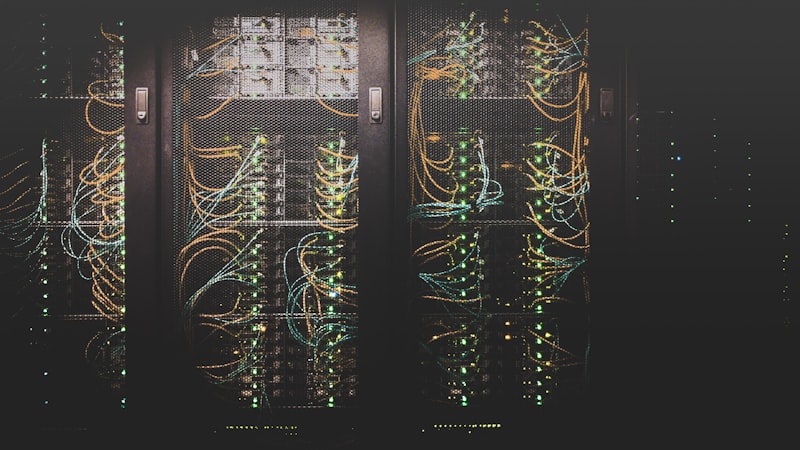
 Cybersecurity
CybersecurityThe Cybersecurity Information Sharing Act of 2015 has been a cornerstone of national cybersecurity policy. Its …
 Cybersecurity
CybersecurityProtecting critical infrastructure from fast flux attacks. Learn about this DNS evasion technique and how service …
 Cybersecurity
CybersecurityAttackers have exploited a critical RCE vulnerability in the Gladinet CentreStack platform. This highlights the …
 Cybersecurity
CybersecurityRecent intelligence reveals an alarming surge in sophisticated cyber threats targeting critical infrastructure sectors. …
 Cybersecurity
CybersecurityCritical infrastructure faces growing cyber threats. This blog delves into the changing risks and highlights essential …
 AI
AIAI's rapid adoption outpaces awareness of its hidden risks. This blog unpacks evolving threats and equips you with …
 Cybersecurity
CybersecurityProtect your community from cyberattacks! This guide offers practical tips and resources to enhance online safety and …